Real-time threat detection is critical for protecting cloud environments as security threats grow more complex. This article evaluates six leading platforms - AccuKnox, CrowdStrike Falcon XDR, SentinelOne Singularity XDR, Palo Alto Networks Cortex XSIAM, Microsoft Defender XDR with Sentinel, and Trend Micro Vision One - focusing on detection speed, accuracy, and integration capabilities. Here's a quick summary:
- AccuKnox: Specializes in Zero Trust for Kubernetes and containers, offering fast detection and a 99.9% accuracy rate. Best for container-heavy environments.
- CrowdStrike Falcon XDR: Excels in endpoint security with lightweight agents and 100% detection accuracy. Ideal for endpoint and cloud workload integration.
- SentinelOne Singularity XDR: Provides autonomous threat response with AI-powered detection and rollback capabilities. Great for automated responses but may need additional tools for broader cloud context.
- Palo Alto Networks Cortex XSIAM: Designed for large SOCs with 10,000+ detectors and advanced automation. High complexity but excellent for large enterprises.
- Microsoft Defender XDR with Sentinel: Cost-effective for Microsoft users, with 79% fewer false positives and robust multi-cloud integrations.
- Trend Micro Vision One: Offers multi-layer protection across endpoints, identity, and cloud. Strong in multi-cloud environments but lacks depth in niche areas.
Each tool has unique strengths suited for specific use cases. Choose based on your environment, team needs, and budget.
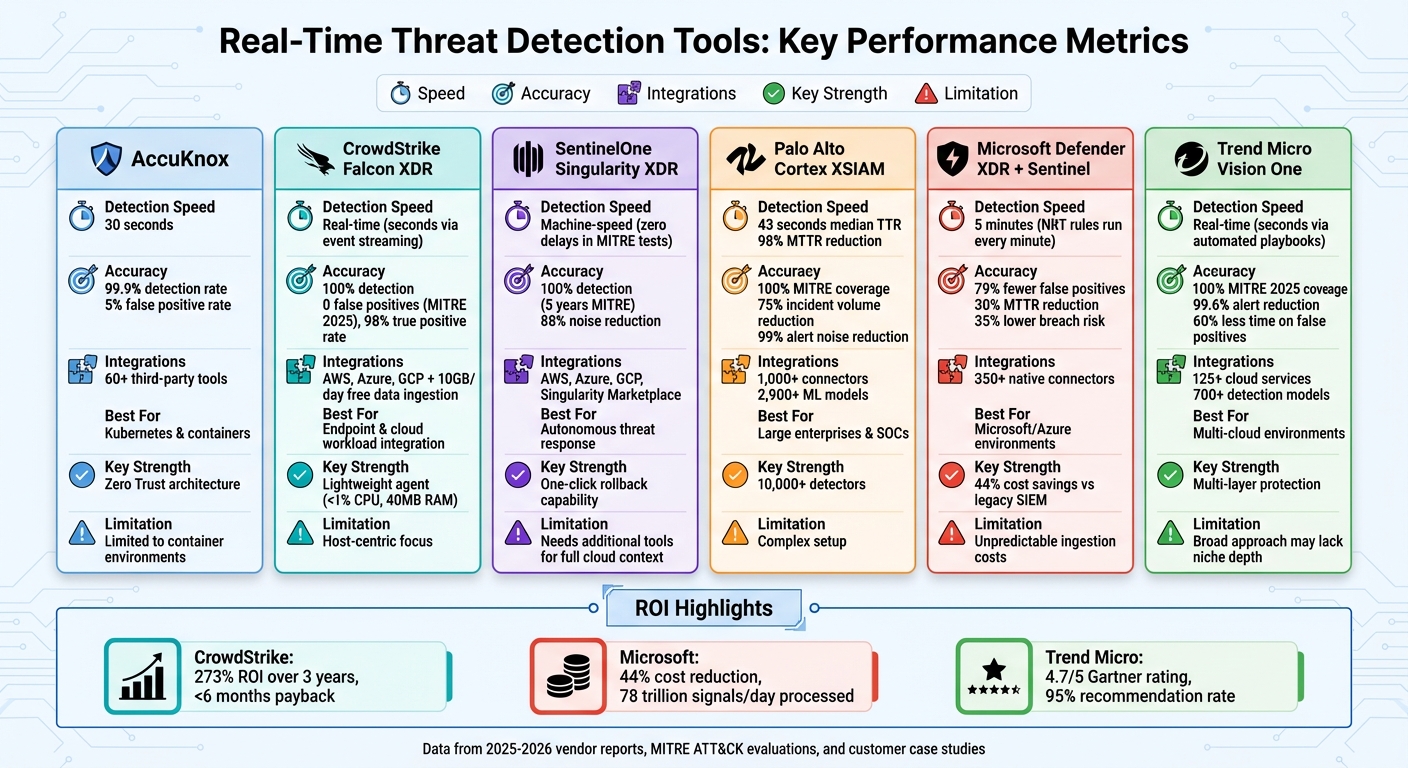
Real-Time Threat Detection Tools Comparison: Speed, Accuracy, and Integration
Built for Speed: Real-Time Cloud Threat Detection
sbb-itb-5174ba0
1. AccuKnox for Zero Trust Cloud Threat Detection
AccuKnox takes a different approach to cloud security by building Zero Trust principles right into its core design. Instead of depending on perimeter defenses alone, it uses advanced kernel-level monitoring to keep an eye on Kubernetes pods, containers, VMs, and serverless functions. This gives the platform deep visibility, allowing it to block threats in real time before they can spread. Here's a closer look at how AccuKnox stands out in key areas.
Detection Speed
AccuKnox reacts swiftly - within just 30 seconds. Its use of real-time telemetry allows it to detect new threats immediately and enforce policies to block unauthorized processes or network connections.
Accuracy
With a 99.9% detection rate and only a 5% false positive rate, AccuKnox significantly outperforms traditional tools, which often exceed a 60% false positive rate. By combining behavioral analytics with allow-based (whitelisting) policies, the platform can effectively separate legitimate activity from real threats, helping security teams focus on what truly matters.
Integration Capabilities
AccuKnox integrates seamlessly with over 60 third-party enterprise tools, including messaging platforms, ticketing systems, and API connectors. It works with major public and private clouds, as well as popular CI/CD and Infrastructure-as-Code platforms. Acting as a command center for SOCs, it also connects with SIEM solutions like Splunk, QRadar, and ArcSight to speed up incident response workflows.
2. CrowdStrike Falcon XDR for Endpoint and Cloud Integration
CrowdStrike Falcon XDR bridges the gap between traditional endpoint security and modern cloud environments with its unified architecture. Using a single lightweight agent, it provides visibility across endpoints, cloud workloads, and containers. Its 1-Click XDR feature automatically detects unprotected cloud workloads - like AWS EC2 instances - and deploys the Falcon agent instantly to secure them. For environments without agents, it uses agentless snapshot scanning to incorporate vulnerability data into unified attack path visualizations. This approach not only simplifies endpoint security but also integrates seamlessly with cloud workloads, focusing on real-time threat detection across different environments.
Detection Speed
Falcon XDR's unified architecture ensures threats are identified immediately. Unlike many solutions that rely on log batch processing, which can take 15 minutes or more, Falcon's event streaming technology delivers alerts in seconds. This speed is critical, especially as cloud exploitation cases surged by 95%, and targeted attacks nearly tripled. Elia Zaitsev, CrowdStrike's Chief Technology Officer, highlighted this urgency:
Real-time security is the difference between stopping a breach and needing incident response – every second counts. Today's adversary moves fast and across domains, and defenders can't afford to waste time waiting for cloud logs to process or detections to populate.
Accuracy
Falcon XDR pairs its speed with exceptional accuracy. It achieved 100% detection with zero false positives in both the 2025 MITRE ATT&CK Enterprise Evaluations and the October 2025 SE Labs Ransomware test. Its Charlotte AI demonstrates over 98% accuracy in autonomous triage decisions, rivaling human experts. In January 2026, Orica, a global manufacturing company, reduced its mean time to respond by 95%, slashing triage time from 4 hours to under 10 minutes. Brett Fernicola, Senior Director of Security Operations at Anywhere Real Estate, shared:
Having experts from Falcon Adversary OverWatch for 24/7 threat hunting provides peace of mind. Alerts dropped dramatically, with 98% confirmed as true positives. There's no noise, no junk.
The lightweight agent is also highly efficient, using less than 1% CPU and only 40MB of RAM, ensuring top-notch accuracy without impacting system performance.
Integration Capabilities
Falcon XDR integrates effortlessly with major cloud providers like AWS, Azure, and GCP. It also includes 10GB per day of free third-party data ingestion from sources such as email, web, CASB, network, identity, and firewalls. The CrowdXDR Alliance establishes a standardized data schema, enabling smooth information sharing across partner tools. Gaurav Verma, Head of IT Risk and Security at Monvia, implemented Falcon Cloud Security to monitor Kubernetes services, reporting that 90% of alerts were resolved automatically. The native Falcon Fusion SOAR further enhances efficiency by orchestrating security workflows and automating repetitive response tasks, eliminating the need for additional tools. According to a Forrester Total Economic Impact study from January 2026, organizations using Falcon XDR saw a 273% ROI over three years, with a payback period of less than six months.
3. SentinelOne Singularity XDR for Autonomous Cloud Workloads
SentinelOne Singularity XDR is designed to protect cloud workloads - like virtual machines, containers, and Kubernetes clusters - by autonomously stopping unauthorized processes. It uses a lightweight, eBPF-based agent for Linux and Kubernetes, which avoids kernel dependencies to maintain system performance and prevent disruptions. Its patented Storyline™ technology tracks and connects event data in real time, reconstructing attack sequences as they unfold. This approach eliminates the need for manual scripts, replacing them with AI-powered decisions made at machine speed. The platform focuses on speed, precision, and smooth integration with cloud environments.
Detection Speed
When it comes to detecting threats, Singularity XDR stands out. Over the past five years, it has consistently achieved zero detection delays during MITRE Engenuity ATT&CK evaluations. Unlike traditional tools that rely on manual intervention, its AI-powered static and behavioral detection engines identify threats instantly. To streamline response efforts, the integrated Purple AI feature automatically generates event summaries, helping prioritize high-risk incidents efficiently.
Accuracy
Singularity XDR has demonstrated perfect detection accuracy in MITRE ATT&CK evaluations for five straight years, identifying every attack technique across all operating systems. It also reduces noise by 88% compared to the average among other security vendors, significantly cutting down on alert fatigue. By collecting telemetry from endpoints, cloud environments, identity sources, and third-party tools into a unified data lake, the platform enables effective cross-surface threat correlation. Its Storyline Active Response (STAR) feature allows users to create custom detection logic that triggers automated responses under specific conditions. SentinelOne’s recognition as a Leader in the 2025 Gartner Magic Quadrant for Endpoint Protection Platforms and its 97% "willingness to recommend" rating on Gartner Peer Insights further highlight its reliability.
Integration Capabilities
Singularity Cloud Workload Security provides real-time protection across AWS, Azure, Google Cloud Platform, and private data centers. Through the Singularity Marketplace, users can access pre-built integrations that enable automated responses across their technology ecosystem. For instance, SentinelOne integrates with Cisco XDR, allowing Singularity detections to enhance incident analytics, support threat hunting, and enable actions like host isolation or file hash blocking directly in the Cisco interface. The platform also offers patented one-click rollback and precise remediation to undo unauthorized changes and restore workloads automatically. SentinelOne telemetry can be centralized in Datadog Cloud SIEM for unified visibility, with 365 days of data retention for malware and fileless attacks. Additionally, the Cloud Funnel feature allows users to replicate high-volume telemetry to cloud storage services like Amazon S3 or Google Cloud Storage for long-term threat analysis.
4. Palo Alto Networks Cortex XSIAM for AI-Powered SOC Analytics
Palo Alto Networks Cortex XSIAM reshapes the way security operations centers (SOCs) function by combining multiple security tools into one streamlined platform. Unlike older systems that depend on manual correlation and custom queries, XSIAM uses over 10,000 detections and 2,900+ machine learning models to automatically gather, link, and standardize raw telemetry from endpoints, networks, identity systems, and cloud environments. Its autonomous AI works within predefined enterprise guidelines, triggering automated playbooks instantly when threats are detected.
Detection Speed
Cortex XSIAM is designed to dramatically speed up threat detection and response. At CBTS, where Chris DeBrunner serves as VP of Security Operations, the platform has delivered exceptional results. DeBrunner shared:
Every single incident gets touched by automation and it's triaged and closed usually within 30 seconds. The XSIAM platform has been very, very helpful with our SOC operations.
The Oneida Nation reported an impressive median time to resolution (MTTR) of just 43 seconds. Across various deployments, XSIAM has demonstrated a 98% reduction in MTTR, cutting response times down to just minutes.
Accuracy
Cortex XSIAM achieved 100% detection coverage during the 2024 MITRE ATT&CK Round 6 evaluation. Its SmartScoring engine assigns risk levels and provides detailed context, enabling analysts to focus on the most critical threats quickly. By consolidating related alerts into unified incidents, the platform significantly reduces the workload for analysts - cutting incident volumes by 75% and reducing alert noise by up to 99%. One specialty retailer experienced an 80% improvement, dropping manually reviewed alerts from 25,000 per quarter to just 4,500, all thanks to enhanced alert correlation. These features align XSIAM with the integrated strategies seen in other advanced cloud analytics platforms.
Integration Capabilities
XSIAM excels in unifying data sources while being far more cost-effective than traditional SIEM solutions. It comes with over 1,000 out-of-the-box connectors for seamless integration with AWS, Azure, Google Cloud Platform, and SaaS tools like Microsoft 365 and Google Workspace. The Cortex Extended Data Lake (XDL) centralizes data from on-premises and cloud environments, eliminating the inefficiencies of switching between multiple tools. The 3.0 release introduced the Cloud & SOC Command Center, which pinpoints posture risks and runtime threats in a single interface. XSIAM also includes tailored analytics for cloud provider logs and security alerts, offering real-time insights across hybrid infrastructures. Companies report achieving robust data coverage at half the cost of older SIEM systems.
5. Microsoft Defender XDR and Sentinel for Azure Analytics
Microsoft Defender XDR and Sentinel combine the capabilities of XDR (Extended Detection and Response) and SIEM (Security Information and Event Management) into a single, streamlined security operations platform. Designed for Azure and multi-cloud setups, this solution processes an astounding 78 trillion signals daily from endpoints, identities, email, and cloud applications to identify potential threats. Like other platforms discussed, it prioritizes speed, precision, and smooth integration across cloud environments.
Detection Speed
Microsoft Sentinel leverages Near-Real-Time (NRT) analytics rules, running queries every minute with a one-minute lookback window. For even quicker threat detection, custom detections analyze events in-stream, cutting out delays entirely. This means incidents can appear in the system within just five minutes. The platform's Fusion correlation engine automatically links related alerts from various components into unified incidents in real time, with any updates to incident status or ownership instantly reflected across both the Microsoft Defender and Azure portals. These features ensure threats are detected and acted upon with minimal delay.
Accuracy
The Fusion correlation engine employs advanced machine learning to transform low-quality alerts into actionable incidents, focusing on identifying complex, multistage attacks. Organizations using Microsoft Sentinel have reported impressive results, including a 79% reduction in false positives and a 35% lower chance of experiencing a data breach. Additionally, the platform's AI assistant, Security Copilot, has been shown to reduce the mean time to resolution (MTTR) for incidents by 30%. Masaki Onishi, Director of Security Operations Division at NTT Communications, highlighted the platform's impact:
By ingesting logs and alerts from our security solutions into Microsoft Sentinel, we can correlate threat analysis from multiple sources. This automation saves valuable time to resolve incidents.
Integration Capabilities
Microsoft Sentinel integrates seamlessly with the Microsoft Defender portal, offering a unified interface for all security operations. It supports over 350 native connectors, enabling visibility across multicloud and multiplatform environments. A key feature is the Defender XDR connector, which streams incidents, alerts, and advanced hunting events directly into Sentinel. While alerts and incidents from Defender XDR are ingested at no extra cost, raw advanced hunting data incurs standard ingestion fees. Chunqui Chen, Director of IT Monitoring and Security Operations Center at Danfoss, praised the platform's simplicity:
Setting up Microsoft Sentinel to ingest logs from 20 applications and thousands of devices was a very simple thing.
In addition to its ease of use, the platform offers 44% lower costs compared to traditional SIEM solutions and includes a default data retention period of 90 days. However, it's worth noting that starting March 31, 2027, Microsoft Sentinel will only be accessible through the Microsoft Defender portal, as Azure portal support will be discontinued. This transition underscores the platform's focus on delivering a unified, real-time threat detection experience for modern cloud ecosystems.
6. Trend Micro Vision One for Multi-Layer Cloud Coverage
Trend Micro Vision One takes a broad approach to cloud security by simultaneously monitoring multiple layers, including endpoint, identity, network, and cloud. It supports over 125 cloud services and utilizes more than 700 detection models to transform overwhelming "cloud noise" into actionable insights.
Detection Speed
The platform's Cloud Intrusion Prevention System (IPS) works seamlessly with cloud-native tools like AWS Network Firewall, stopping malware and vulnerabilities in real time before they can compromise business applications. Automated playbooks take swift action, isolating endpoints and blocking malicious traffic in just seconds. Meanwhile, real-time decryption and inspection occur across both public and private cloud environments. For containerized applications, Vision One continuously tracks network activity, tracing connections to suspicious IPs or command-and-control servers. Additionally, its agentless scanning capabilities allow for vulnerability and malware detection across major cloud providers, eliminating the performance strain often caused by traditional agents.
Accuracy
Trend Micro Vision One has proven its effectiveness, achieving 100% analytic coverage and protection during the 2025 MITRE ATT&CK Evaluations (Enterprise Round 7). Automated threat correlation and prioritization have helped organizations cut daily alerts by 99.6% and reduce the time spent on false positive investigations by 60%. For instance, in 2025, the Northeast Georgia Health System reported this 60% time savings, enabling their team to focus on critical threats rather than manual alert management. The platform’s AI-powered analytics also identify emerging threats and vulnerabilities up to three months before official vendor patches are released, thanks to the Trend Zero Day Initiative. These capabilities enhance its already strong integration and detection features.
Integration Capabilities
Vision One integrates with tools like AWS CloudTrail to monitor privilege escalation and S3 data exfiltration, as well as with platforms such as Tenable, SentinelOne, and Microsoft Defender. Dr. Andrew Adams, Associate Manager of Information Security at Xsolis, highlighted its value:
The cloud posture tool is key to helping us define misconfigurations and helping us ensure that we align with HIPAA and HITRUST and the NIST cybersecurity framework.
The platform also offers API-driven file analysis and direct response options, such as isolating endpoints or revoking user identities directly from the console. These integrations enhance detection and incident response capabilities, reinforcing the platform’s focus on speed and precision. With a 4.7/5 rating on Gartner Peer Insights from 129 reviews as of March 3, 2026, and 95% of users recommending it, Vision One has been recognized as a Leader in the IDC MarketScape for Worldwide Exposure Management 2025. To top it off, the TrendAI Flex licensing model uses a flexible, credit-based system that allows organizations to reallocate credits across 30+ Vision One solutions as their security demands change.
Pros and Cons
Here’s an overview of how each tool performs in terms of detection speed, accuracy, and integration, along with their key advantages and challenges. This breakdown complements the detailed metrics and integration capabilities discussed earlier.
| Tool Name | Detection Speed | Accuracy | Integration Capabilities | Pros | Cons |
|---|---|---|---|---|---|
| AccuKnox | Real-time (eBPF) | High (Behavioral) | Kubernetes, Hybrid Cloud | Focus on Zero Trust; minimal overhead | Limited to container/Kubernetes environments |
| CrowdStrike Falcon XDR | Real-time | High (AI-driven) | Broad (API-based) | Lightweight agent; top-tier host telemetry | Host-centric; limited cloud control visibility |
| SentinelOne Singularity XDR | Machine-speed | High (AI-driven) | Agent & Agentless | Autonomous threat response; ransomware rollback | Needs additional tools for full cloud context |
| Palo Alto Networks Cortex XSIAM | Real-time | High (10,000+ detectors) | Native SOAR (1,000+ playbooks) | Extensive MITRE mapping; SOC automation | Complex setup; better suited for large enterprises |
| Microsoft Defender XDR & Sentinel | Real-time | 79% fewer false positives | 350+ Connectors | Cost-effective for E5 users; seamless Microsoft integration; 44% cost savings | Unpredictable ingestion costs; Microsoft-focused |
| Trend Micro Vision One | Real-time | High (Cross-layer) | Email, Endpoint, Cloud | Multi-vector coverage; 100% MITRE coverage | Broad approach may lack depth in niche areas |
A Closer Look at Key Tools
Each platform has unique strengths and limitations that cater to specific use cases.
CrowdStrike Falcon XDR shines in endpoint-level detection, offering continuous telemetry and lightweight agents. However, it leans heavily on host and workload-level monitoring, leaving cloud control plane visibility as a weaker point.
SentinelOne Singularity XDR uses AI for autonomous threat responses and ransomware recovery. While effective in its domain, it may require pairing with other tools to provide a complete picture of cloud infrastructure activity.
Palo Alto Networks Cortex XSIAM stands out with its 10,000+ detectors mapped to MITRE ATT&CK and over 1,000 pre-built automation playbooks. This makes it a powerhouse for large-scale SOC operations, though its complexity demands significant technical expertise.
Microsoft Defender XDR and Sentinel offer seamless integration across endpoints, identity, and cloud workloads. With a 44% cost reduction compared to legacy SIEMs and a 79% reduction in false positives, it’s highly efficient for organizations using Microsoft environments. However, its ingestion-based pricing can become unpredictable as cloud use grows.
AccuKnox focuses on Kubernetes environments with its eBPF-based telemetry and Zero Trust architecture. While it performs well in its niche, it doesn’t offer the broader capabilities of multi-cloud platforms.
Trend Micro Vision One delivers multi-layer protection across email, endpoints, and cloud workloads, achieving full analytic coverage in the 2025 MITRE ATT&CK Evaluations. However, its broad coverage may lack the depth needed for certain specialized use cases.
Key Considerations for Selection
When choosing a tool, think about how it handles cross-account activity, ephemeral workloads, and third-party SaaS integrations. These are often the areas where detection gaps emerge. For organizations managing diverse cloud environments, platforms that enrich context by linking identities, permissions, and data sensitivity can transform raw alerts into actionable insights.
Conclusion
Our analysis highlights the diverse strengths of different platforms, emphasizing the importance of choosing a tool that aligns with your specific cloud setup, team dynamics, and operational demands. For organizations deeply rooted in Microsoft ecosystems, Microsoft Defender XDR and Sentinel stand out for their seamless integration with Azure workloads and cost-efficient operations. On the other hand, CrowdStrike Falcon XDR excels in endpoint security with its lightweight agents and robust host telemetry, though it may require supplementary tools to fully cover cloud control planes.
For Kubernetes and container-heavy environments, AccuKnox offers an eBPF-driven Zero Trust framework, while SentinelOne Singularity XDR impresses with its autonomous threat response capabilities. Large enterprises needing extensive automation might lean toward Palo Alto Networks Cortex XSIAM, which boasts over 10,000 detectors. However, its complexity may require a higher level of technical expertise to manage effectively.
"Choosing Microsoft Sentinel enabled a more holistic approach, eliminating a patchwork of vendors." - CIO, Retail
Pricing models also play a pivotal role. While per-GB ingestion pricing can become unpredictable in high-volume scenarios, per-asset pricing often provides a more stable path for scaling as your cloud infrastructure grows. Look for tools that add context by linking identities, permissions, and exposure paths, transforming raw alerts into actionable insights.
For multi-cloud deployments, platforms that unify telemetry across AWS, Azure, and GCP into a standardized schema are essential. Trend Micro Vision One delivers strong multi-layer protection for such environments. Ultimately, the best threat detection solution should combine speed, precision, and integrated cloud analytics to meet the demands of modern cloud security.
FAQs
Which tool fits my cloud stack best (AWS, Azure, GCP, or Kubernetes)?
When it comes to threat detection tools, the right choice often depends on the cloud platform you're using. For AWS, tools like Amazon GuardDuty and Cloudanix are excellent options. If you're working with Azure, Microsoft Sentinel is a strong contender, while Google Cloud Security Command Center is tailored for GCP environments. For Kubernetes setups, Falco is a reliable choice, and if you're managing a multi-cloud environment, Panther offers robust support. The key is to align your tool with your specific cloud provider and security requirements.
How do I estimate total cost when pricing depends on data ingestion?
When figuring out costs for tools with data ingestion-based pricing, start by estimating how much data you'll process. Pricing often depends on factors like data volume (per GB) or number of hosts per month. Don't forget to include potential extra charges for things like storage, retention periods, or add-on features. Taking these into account allows you to better predict costs as your data usage grows, giving you a clearer picture of what you'll spend on real-time threat detection.
Do I need agents, or is agentless scanning enough for real-time detection?
When deciding between agents and agentless scanning, it all comes down to your cloud setup and security priorities. Agentless scanning, which relies on cloud APIs, offers fast deployment and wide coverage - perfect for dynamic workloads like containers. But if you need more in-depth runtime visibility in complex environments, lightweight agents might be the better choice. In many cases, a hybrid approach strikes the right balance: agentless scans handle broad coverage, while agents provide detailed, real-time protection where it matters most.